The Cyber Essentials Plus assessment consists of five test cases, each designed to verify whether key Cyber Essentials controls are operating effectively in practice. Collectively, these tests determine whether the organisation can withstand the common attack methods used by opportunistic, low-skill attackers.
The Five Cyber Essentials Test Cases
The Cyber Essentials Plus assessment consists of five test cases, each designed to verify whether key Cyber Essentials controls are operating effectively in practice. Collectively, these tests determine whether the organisation can withstand the common attack methods used by opportunistic, low-skill attackers.





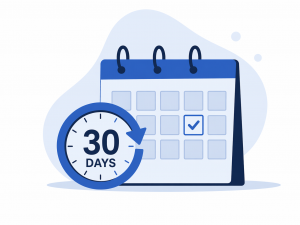
Timing of the CE+ Assessment
The Cyber Essentials Plus audit must be completed within three months of the award of Cyber Essentials certification. To be awarded Cyber Essentials Plus certification, all required tests must be completed and compliance must be demonstrated within a 30-day assessment window.
Test 1: External Vulnerability Assessment
The purpose of the external vulnerability assessment is to identify vulnerabilities that could enable an internet-based opportunistic attacker to gain unauthorised access to your organisation’s systems using common, low-skill methods.
A KEYSIGMA consultant will assess your external IP addresses using our industry-leading, Payment Card Industry (PCI)-compliant vulnerability scanners.
Any vulnerabilities identified on the external infrastructure with a CVSS v3 score of 7.0 or above must be remediated in order to achieve compliance with the standard. Where vulnerabilities are identified, KEYSIGMA will provide guidance on remediation and support your patching efforts by rescanning the external infrastructure until the identified issues have been resolved.
The assessor will review all externally open ports and exposed services, and a full list of the services identified will be provided to the applicant.
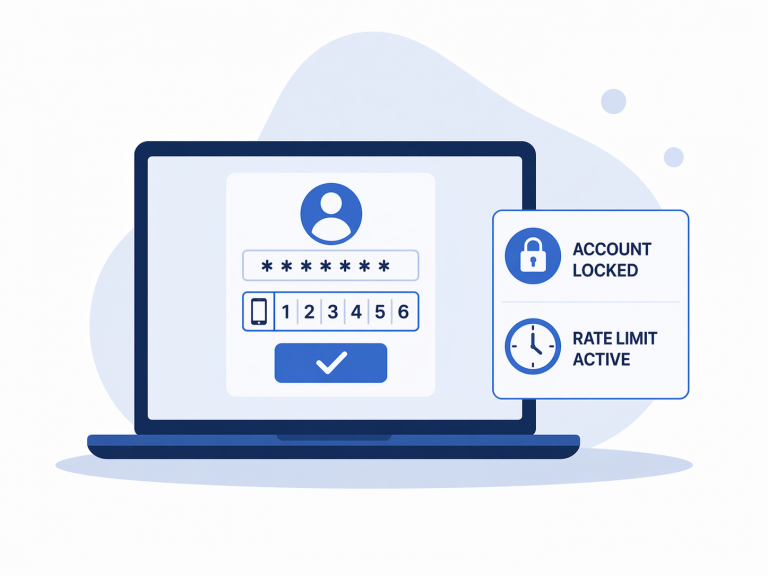
For any service that provides access to non-public or writable information, the Cyber Essentials Plus standard requires protection against brute-force attacks. This must be achieved through one of the following controls:
- the use of multi-factor authentication; or
- the implementation of account lockout or throttling measures that permit no more than one login attempt within a five-minute period.
If neither of these controls can be implemented, the service must be closed to meet the standard. Failure to do so will result in the assessment being unsuccessful.
Tests 2-5 Sampling Methodology
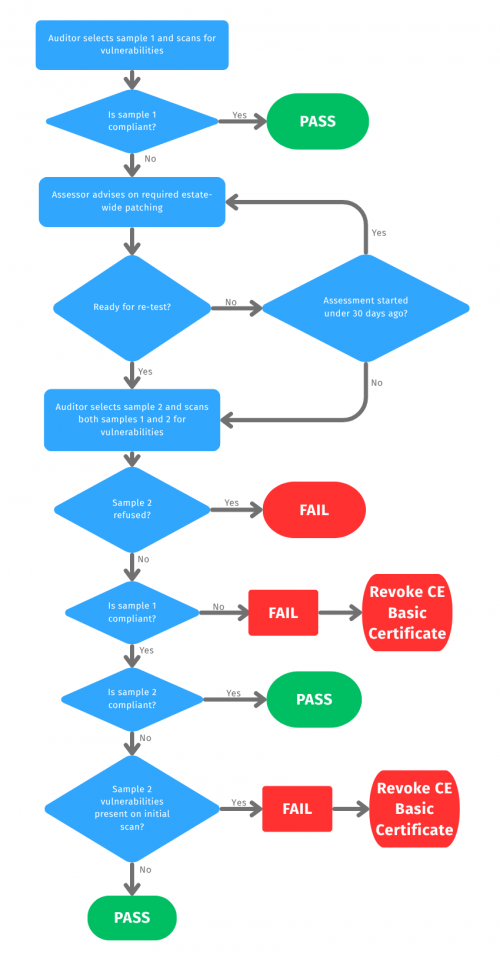
The Cyber Essentials Plus tests 2 to 5 are carried out on a representative sample of devices from the applicant’s estate. KEYSIGMA selects this sample to reflect the operating systems and build types in use, with all devices chosen at random no more than three working days before the assessment.
The initial sample, Sample 1, is assessed against all five Cyber Essentials Plus test cases. Where non-compliances are identified, the applicant may remediate the vulnerabilities discovered, provided this is completed on the sampled devices within the 30-day assessment window. KEYSIGMA will aim to provide advice and guidance to assist with remediation.
Following remediation, the scheme requires a second sample of the same size to be selected using the same sampling methodology, in order to confirm that remediation has been applied consistently across the estate.
To achieve certification, both Sample 1 and Sample 2 must be assessed and found compliant with all test requirements within the 30-day assessment window.
Test 2: Internal Vulnerability Assessment
The Cyber Essentials Plus standard requires a representative sub-sample of internal assets to undergo vulnerability scanning using KEYSIGMA’s industry-leading, Payment Card Industry (PCI)-compliant vulnerability scanners.
The purpose of this testing is to confirm that the organisation is complying with the Cyber Essentials patching requirements.
To meet the standard, the assessment must not identify any vulnerabilities rated with a CVSSv3 score of 7.0 or above within the selected sample.
Where vulnerabilities are identified, KEYSIGMA will endeavour to provide advice and guidance to support remediation. Any corrective actions must be implemented across the entire estate, rather than only on the sampled devices.
All corrective actions must be completed within the 30-day assessment window. Failure to achieve compliance on the initial sample within this timeframe will result in the assessment being unsuccessful.
Once the non-compliances identified in Sample 1 have been remediated, a second sample will be selected at random to verify that the issues identified in the initial sample have been remediated consistently across the entire estate.
KEYSIGMA will also assess the security of your mobile devices by reviewing screenshots collected from the devices within your sample set. These checks will confirm that all sampled devices are:
- supported by the vendor;
- fully up to date and configured to apply security patches automatically;
- restricted to downloading applications only from official app stores;
- free from untrusted user-installed certificates.
Please note:
- jailbroken iPhones are non-compliant; and
- sideloaded applications are non-compliant.
Test 3: Malware Protection Assessment
The Cyber Essentials Plus assessment requires the assessor to confirm that anti-malware software is installed on all sampled devices, is supported by the vendor, fully up to date, and configured in accordance with the vendor’s instructions and guidance. The assessment also evaluates the effectiveness of these controls against malware delivered through common attack vectors.
a) Malware delivery by email
KEYSIGMA will send pseudo-malware files to the applicant’s mail server. A pass is achieved where the files are either not received or, if received, cannot be opened from the user’s mailbox.
b) Malware delivery through browsers
The assessor will attempt to access pseudo-malware files through all browsers installed on the device. A pass is achieved where the files cannot be opened.
Test 4: Multifactor Authentication Configuration Asessment
The Cyber Essentials Plus standard includes multi-factor authentication (MFA) checks to verify that MFA has been enabled on all declared services where it is available.
Ideally, this should be evidenced through a global configuration that makes MFA mandatory for all users, or through Single Sign-On (SSO) with MFA enforced. Where this cannot be demonstrated centrally, the KEYSIGMA assessor will verify MFA for sampled users and administrators across all relevant services.
A pass is achieved where the user(s) and administrator(s) arerequired to complete a compliant form of MFA before access is granted.
Please note that location-based controls, including IP whitelisting, are no longer recognised as a compliant form of MFA.
Test 5: Account Seperation Asessment
The Cyber Essentials Plus standard requires the separation of user and administrative accounts. Low-privilege user accounts should be used for day-to-day activities, while administrative accounts should be reserved for administrative duties only.
This control is important because, if a user inadvertently downloads a malicious file and an attacker compromises the device, administrative privileges would give the attacker immediate control of the system. Where the user account is configured as a standard, low-privilege account, the attacker would instead need to carry out a privilege escalation attack to gain further access, which requires a higher level of technical capability.
To verify account separation during the Cyber Essentials Plus assessment, KEYSIGMA consultants will attempt to run administrative processes using standard user accounts.
A pass is achieved if the user is prompted for separate administrative credentials and the process cannot be executed using the standard user account alone.
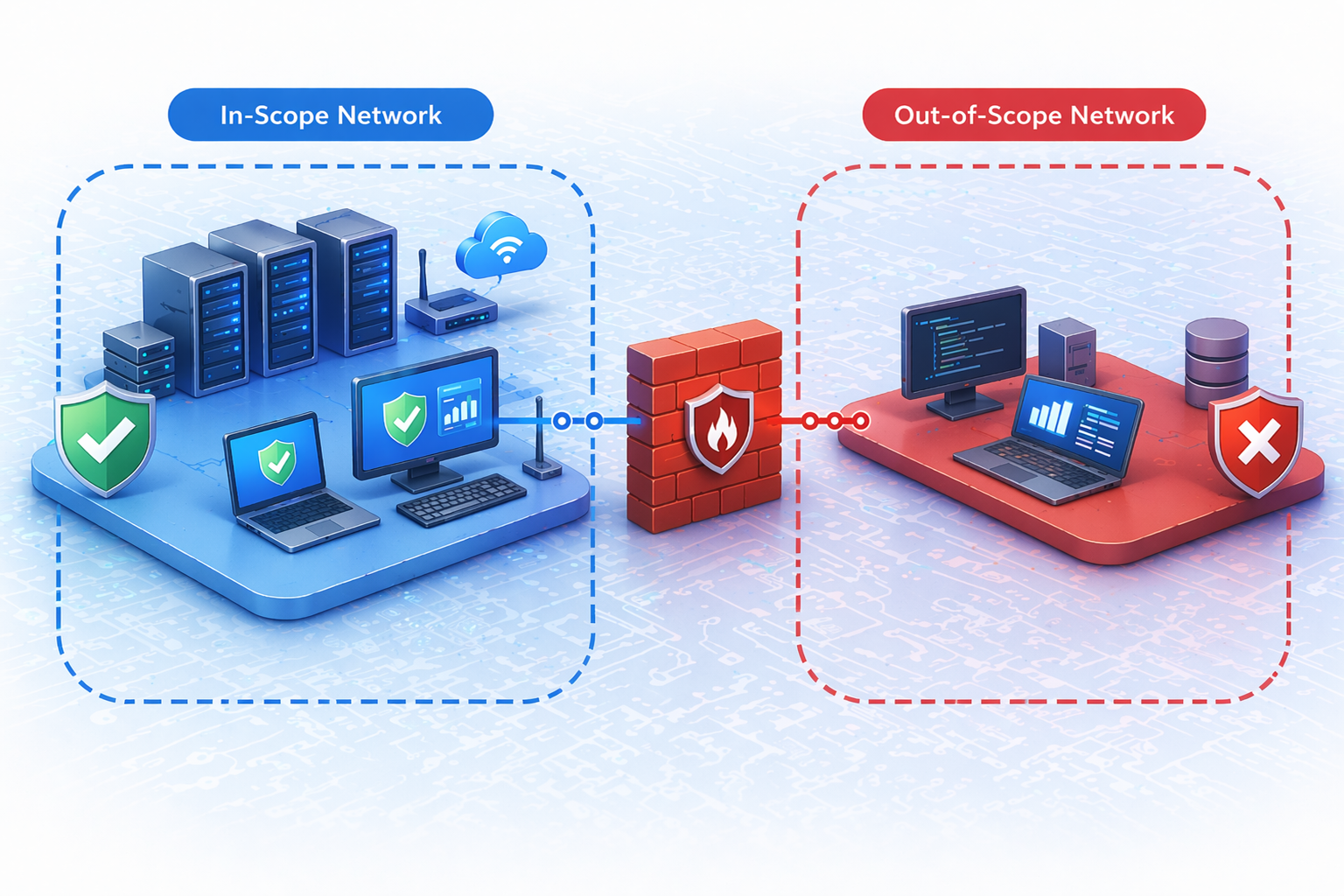
De Scoped Networks
The Cyber Essentials basic process allows organisations to de-scope networks from the Cyber Essentials standard.
Where an assessment does not cover the whole organisation:
- Segregation must be enforced using either a physical firewall or VLANs.
Where network segments have been de-scoped from the assessment, the partial scope and compliant segregation will be technically verified during the Cyber Essentials Plus assessment by the KEYSIGMA auditor.