Cyber Essentials Plus:
A Technical Audit of Your IT Systems
Cyber Essentials Plus is the highest level of certification available under the Cyber Essentials scheme. It is a more rigorous assessment of your organisation’s cyber security systems, designed to independently verify that your controls are in place and operating effectively.
By testing your environment in practice, Cyber Essentials Plus certification provides assurance to customers, partners, and stakeholders that your organisation has adequate protection against the most common cyber threats.
The Five Cyber Essentials Test Cases
The Cyber Essentials Plus assessment consists of five test cases, each designed to verify whether key Cyber Essentials controls are operating effectively in practice. Collectively, these tests determine whether the organisation can withstand the common attack methods used by opportunistic, low-skill attackers.





Get Ready for the 26 April 2026 Transition
The new version of the Cyber Essentials standard, Danzell, takes effect on 26 April. This introduces major changes to the sampling regime and the patching requirements that must be demonstrated during the assessment. The sampling and retesting methodology is explained below.
Sampling Methodology
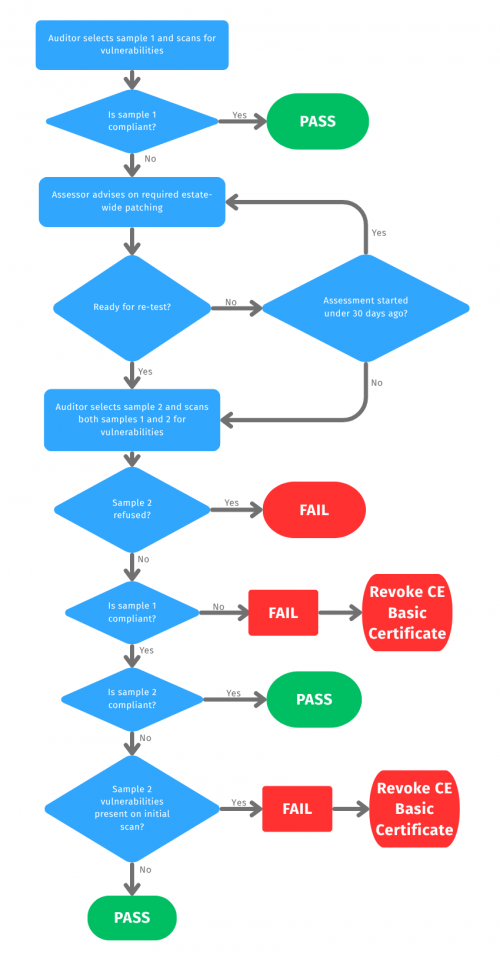
The Cyber Essentials Plus assessment is based on a representative sample of devices from the Applicant’s estate. KEYSIGMA selects this sample to reflect the operating systems and build types in use, with all devices chosen at random no more than three working days before the assessment.
The initial sample, Sample 1, is tested against all five Cyber Essentials Plus test cases. Where any non-compliances are identified, these must be remediated across the entire estate, not just on the sampled devices.
A second randomly selected validation sample, Sample 2, is then chosen to confirm that remediation has been applied consistently across the estate. To pass the assessment, both Sample 1 and Sample 2 must be retested and found compliant with all test requirements within the 30-day assessment window.
De Scoped Networks
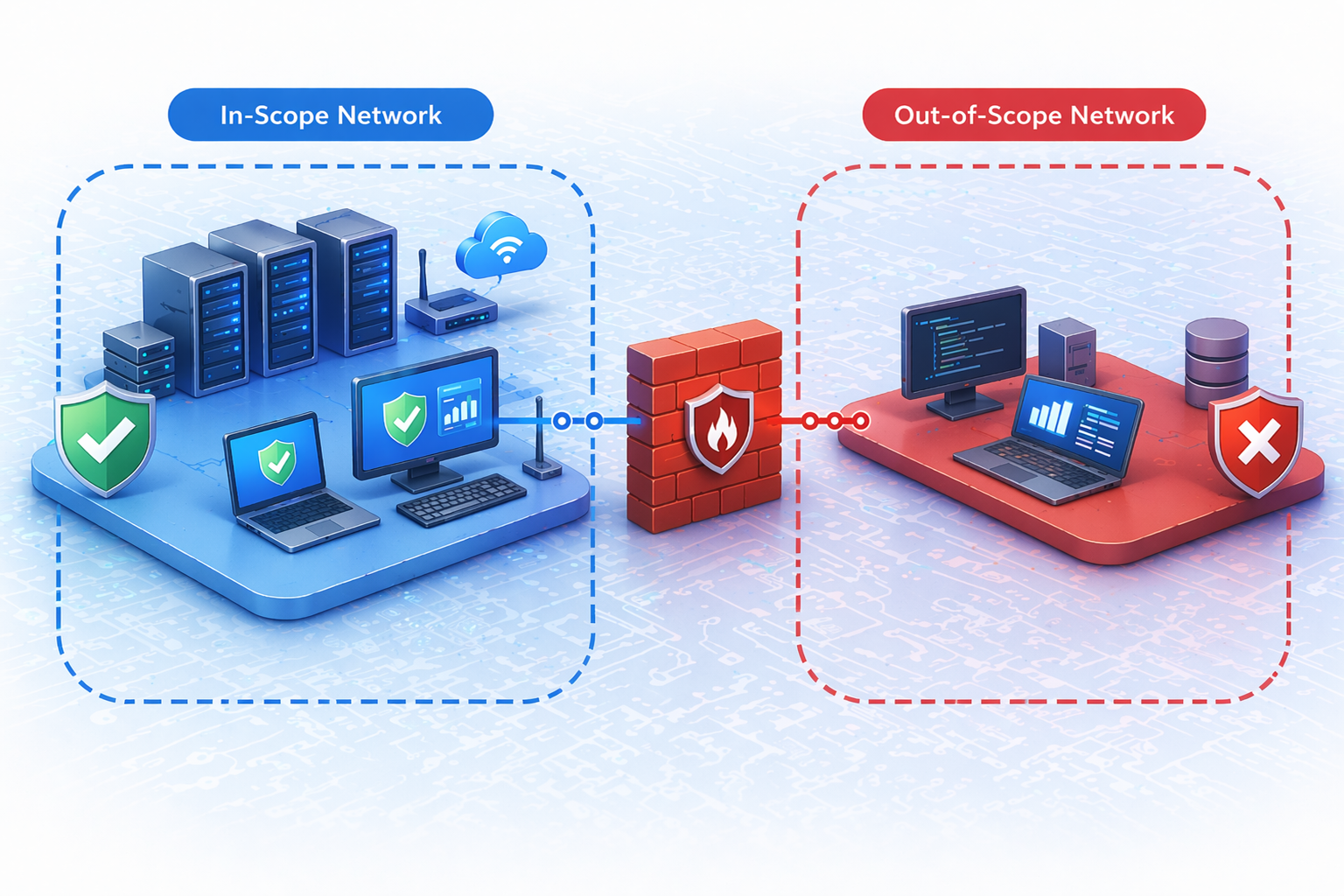
The Cyber Essentials basic process allows organisations to de-scope networks from the Cyber Essentials standard.
Where an assessment does not cover the whole organisation:
- Segregation must be enforced using either a physical firewall or VLANs.
Where network segments have been de-scoped from the assessment, the partial scope and compliant segregation will be technically verified during the Cyber Essentials Plus assessment by the KEYSIGMA auditor.

Account Seperation

Maware Protection

Multi-factor Authentication

External Vulnerability Assessment

Internal Vulnerability Assessment
The Five Cyber Essentials Test Cases
The Cyber Essentials Plus assessment consists of five test cases, each designed to verify whether key Cyber Essentials controls are operating effectively in practice. Collectively, these tests determine whether the organisation can withstand the common attack methods used by opportunistic, low-skill attackers.