Get Ready for the 26 April 2026 Transition
Understanding the Cyber Essentials Danzell Standard
The National Cyber Security Centre (NCSC) and IASME Consortium have announced that the current Willow version of the standard will be replaced by Danzell. This is important to keep the Cyber Essentials controls effective at protecting organisations against common cyber attacks.
All assessments started from 26 April 2026 onwards will be assessed against the new Danzell standard.
Vulnerability Fixes
Danzell does not change the underlying requirement to remediate vulnerabilities; however, it clarifies and makes the definition more explicit. A “vulnerability fix” now clearly includes any vendor-approved method used to remediate a known issue. This includes:
- Patches.
- Updates.
- Registry changes.
- Configuration changes.
- Scripts.
- Any other vendor-approved remediation mechanism.
Where remediation requires multiple actions, (for example, a patch combined with a configuration change) then all elements must be applied for the fix to be considered complete.
Firewalls and Routers Must Receive Vulnerability Fixes
The Danzell standard now makes clear that the operating systems running on firewalls and routing devices must be treated in the same way as any other in-scope operating system.
This means all Cyber Essentials requirements for supported software and security updates apply equally to these network devices. They must be vendor-supported, kept up to date with security patches and vulnerability fixes, and have all relevant updates applied within 14 days of release.
Vulnerability Fix Timeframes and Danzell Compliance
Security updates must be installed within 14 days of release where:
- The vendor rates the vulnerability as critical or high risk
- The vulnerability has a CVSS v3 base score of 7.0 or above
- The vendor does not provide a severity rating
Failure to meet these requirements will result in an automatic assessment failure in Danzell.
These clarifications reinforce the importance of timely patching, as delayed security updates remain one of the most common causes of successful cyber attacks.

Vulnerability Fixes
Danzell does not change the underlying requirement to remediate vulnerabilities; however, it clarifies and makes the definition more explicit. A “vulnerability fix” now clearly includes any vendor-approved method used to remediate a known issue. This includes:
- Patches.
- Updates.
- Registry changes.
- Configuration changes.
- Scripts.
- Any other vendor-approved remediation mechanism.
Where remediation requires multiple actions, (for example, a patch combined with a configuration change) then all elements must be applied for the fix to be considered complete.
Vulnerability Fix Timeframes and Danzell Compliance
Security updates must be installed within 14 days of release where:
- The vendor rates the vulnerability as critical or high risk
- The vulnerability has a CVSS v3 base score of 7.0 or above
- The vendor does not provide a severity rating
Failure to meet these requirements will result in an automatic assessment failure in Danzell.
These clarifications reinforce the importance of timely patching, as delayed security updates remain one of the most common causes of successful cyber attacks.
Firewalls and Routers Must Receive Vulnerability Fixes

The Danzell standard now makes clear that the operating systems running on firewalls and routing devices must be treated in the same way as any other in-scope operating system.
This means all Cyber Essentials requirements for supported software and security updates apply equally to these network devices. They must be vendor-supported, kept up to date with security patches and vulnerability fixes, and have all relevant updates applied within 14 days of release.
Danzell now defines a cloud service as: any on-demand, internet-accessible service used to store or process organisational data. In practice, if a service handles your organisation’s data, it is in scope.
Social media accounts are now also explicitly included within the scope of the Cyber Essentials Danzell assessment, reflecting the real operational and reputational risks they can present if compromised.
Multi-factor authentication (MFA) is mandatory on all cloud services where it is available, even where this comes at an additional cost. If MFA is offered but not enabled, this will result in an automatic assessment failure.
Organisations must also ensure that all cloud services are fully declared, including any “shadow IT” adopted outside formal IT oversight.
What Danzell Means for Cloud Services
Danzell now defines a cloud service as: any on-demand, internet-accessible service used to store or process organisational data. In practice, if a service handles your organisation’s data, it is in scope.
Social media accounts are now also explicitly included within the scope of the Cyber Essentials Danzell assessment, reflecting the real operational and reputational risks they can present if compromised.
Multi-factor authentication (MFA) is mandatory on all cloud services where it is available, even where this comes at an additional cost. If MFA is offered but not enabled, this will result in an automatic assessment failure.
Organisations must also ensure that all cloud services are fully declared, including any “shadow IT” adopted outside formal IT oversight.
Scoping
- Where an assessment does not cover the whole organisation:
- The scope description must state which networks are not in the scope of the assessment.
- The segregations must be enforced using either a physical firewall or a VLAN(s).
- Scope exclusions only apply at the network level, not the device level. Individual devices cannot be excluded unless connected to a de-scoped network.
- Details of the excluded networks must now be defined and documented in the self-assessment questionnaire. This information is required for certification purposes but will not be made public on the certificate.

Scoping

- Where an assessment does not cover the whole organisation:
- The scope description must state which networks are not in the scope of the assessment.
- The segregations must be enforced using either a physical firewall or a VLAN(s).
- Scope exclusions only apply at the network level, not the device level. Individual devices cannot be excluded unless connected to a de-scoped network.
- Details of the excluded networks must now be defined and documented in the self-assessment questionnaire. This information is required for certification purposes but will not be made public on the certificate.

Descoping
The Danzell standard clarifies two important principles relating to cloud services and the devices used to access them:
- All cloud services fall within scope, even when they are accessed solely from a segregated or descoped network.
- Any device used to access cloud services is also in scope, even when connected to a descoped network.
This means a device can now only be descoped from Cyber Essentials if it either:
- has no internet access, or
- is only connected to a descoped network and does not access any organisational cloud services.
For example, a developer workstation located on a descoped network segment would return to scope if it is used to access corporate cloud platforms such as finance systems, HR applications, or CRM solutions.
Descoping

The Danzell standard clarifies two important principles relating to cloud services and the devices used to access them:
- All cloud services fall within scope, even when they are accessed solely from a segregated or descoped network.
- Any device used to access cloud services is also in scope, even when connected to a descoped network.
This means a device can now only be descoped from Cyber Essentials if it either:
- has no internet access, or
- is only connected to a descoped network and does not access any organisational cloud services.
For example, a developer workstation located on a descoped network segment would return to scope if it is used to access corporate cloud platforms such as finance systems, HR applications, or CRM solutions.
Declaration of Ongoing Compliance
Cyber Essentials still requires a board-level representative to sign off the assessment before submission. That has not changed under Danzell.
What has changed is the declaration itself. The signatory must now formally confirm that the organisation will maintain compliance with all Cyber Essentials controls throughout the full 12-month certification period.
This reinforces a core principle of the scheme: Cyber Essentials is not a one-off exercise, but an ongoing commitment to baseline security.

Declaration of Ongoing Compliance

Cyber Essentials still requires a board-level representative to sign off the assessment before submission. That has not changed under Danzell.
What has changed is the declaration itself. The signatory must now formally confirm that the organisation will maintain compliance with all Cyber Essentials controls throughout the full 12-month certification period.
This reinforces a core principle of the scheme: Cyber Essentials is not a one-off exercise, but an ongoing commitment to baseline security.

Danzell Cyber Essentials Plus Changes
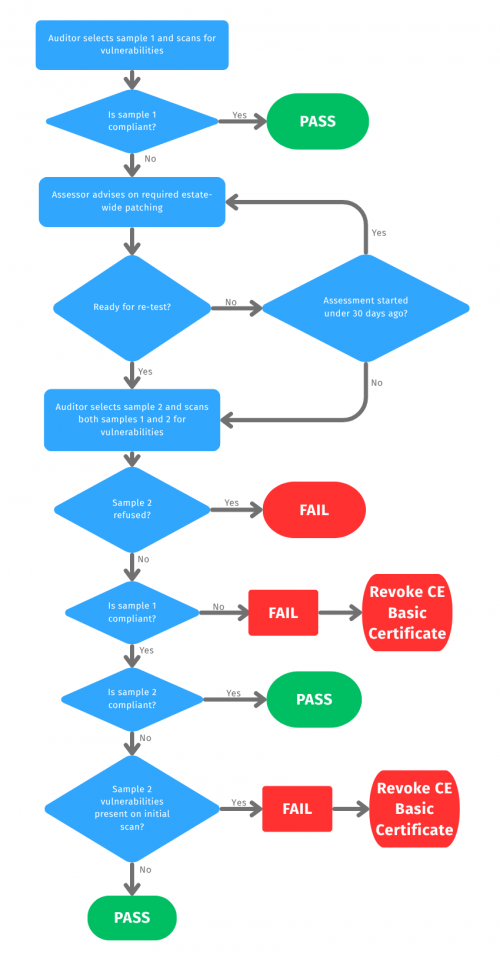
Danzell keeps the same random sampling approach, but now requires evidence that any fixes have been applied across the wider estate, not just the devices tested. If threshold-level vulnerabilities remain, the assessment will fail and Cyber Essentials certification may be withdrawn.
Danzell CE+ Sampling and Retesting Methodology
- The Danzell Cyber Essentials Plus standard retains the same sampling regime as the previous Willow standard.
- All testing samples are chosen at random, by the assessor, no more than 3 working days before the assessment.
- If there are any non-compliances identified on sample 1, these must be remediated across the entire estate and not just the sampled devices .
- To verity the global application of the vulnerability fixes, a second randomly selected validatory sample is chosen (sample 2).
- Both sample 1 and sample 2 are then retested together within the 30 days assessment window.
Danzell CE+ Sampling and Retesting Methodology
- The Danzell Cyber Essentials Plus standard retains the same sampling regime as the previous Willow standard.
- All testing samples are chosen at random, by the assessor, no more than 3 working days before the assessment.
- If there are any non-compliances identified on sample 1, these must be remediated across the entire estate and not just the sampled devices .
- To verity the global application of the vulnerability fixes, a second randomly selected validatory sample is chosen (sample 2).
- Both sample 1 and sample 2 are then retested together within the 30 days assessment window.

Danzell Raises the Bar for Estate-Wide Patch Management
Overall, this change strengthens Cyber Essentials Plus as a true assurance standard by requiring organisations to show that patching and vulnerability management are being applied consistently across the entire estate.
In practice, success under Danzell will depend on strong patch management processes and clear visibility of vulnerabilities across all devices.
For larger environments in particular, it will be difficult to pass a Cyber Essentials Plus assessment without a way to deploy corrective actions at scale, such as through a Mobile Device Management (MDM) solution.
Danzell Raises the Bar for Estate-Wide Patch Management

Overall, this change strengthens Cyber Essentials Plus as a true assurance standard by requiring organisations to show that patching and vulnerability management are being applied consistently across the entire estate.
In practice, success under Danzell will depend on strong patch management processes and clear visibility of vulnerabilities across all devices.
For larger environments in particular, it will be difficult to pass a Cyber Essentials Plus assessment without a way to deploy corrective actions at scale, such as through a Mobile Device Management (MDM) solution.
The KEYSIGMA View of the Changes
KEYSIGMA’s view is that Danzell is a positive tightening of Cyber Essentials. It removes many of the grey areas that previously led organisations (often unintentionally) to under-scope assessments, particularly where self-certification was done without specialist support.
A clear theme runs through the update: tighter scoping and more consistent application of controls. In other words, it’s now harder to “pass on paper” while leaving real gaps in day-to-day security, exactly what a baseline standard should prevent.
We also see Danzell’s clearer scoping model as a step toward future alignment with stackable certification approaches, such as Defence Cyber Certification (DCC), where well-defined boundaries and repeatable evidence matter.
Two clarifications are especially welcome:
Cloud is treated as core infrastructure. Danzell’s clearer cloud definition brings more services into scope, reflecting the reality that many organisations now store and process critical data in SaaS platforms.
Segregation isn’t a free pass. Devices in a segregated (out-of-scope) subset are brought back into scope if they access in-scope cloud services, because allowing lower-assurance devices into core cloud systems would undermine security.
Finally, the strengthened Cyber Essentials Plus methodology is a major improvement. By validating remediation beyond the initial sample, Plus becomes more clearly an assurance standard, which is essential when it’s used for procurement and supplier confidence.
Overall, the direction is clear: organisations will need disciplined patch management, consistent device baselines, and credible visibility of vulnerabilities across the estate.